OAuth 2.0 flow for Web Server applications
Ways of the authorization flow automation
Thank you for reaching out to Sigma Software!
Please fill the form below. Our team will contact you shortly.
Sigma Software has offices in multiple locations in Europe, Northern America, Asia, and Latin America.

USA

Sweden

Germany

Canada

Israel

Singapore

UAE

Australia

Austria

Ukraine

Poland

Argentina

Brazil

Bulgaria

Colombia

Czech Republic

Hungary

Mexico

Portugal

Romania

Uzbekistan
Many of us have at least once faced integrations with 3rd party Services on our projects. We usually test such functionality manually, authorizing through such services as Google accounts and others. When it comes to API auto-tests, it often begs the questions: how can we automate this process? Which way of access token generation brings more benefits in case there is one integration... dozens of integrations?
OAuth 2.0 flow for Web Server applications
Ways of the authorization flow automation
In this article, I would like to describe the main ways of OAuth2 authorization during API tests implementation and their pros and cons. I hope it would be helpful for you.
In many cases the service accounts authorization is enough to get an access token for the tests. However, there are situations when we need to know who is logging in, what permissions the user has, etc. Here we need to use Web Server application authorization, which requires user’s actions. That is why the main topic of this article is OAuth 2.0 for Web Server applications.
In general, OAuth 2.0 flow works as follows:
Basing on the project conditions, we can implement the OAuth2 authorization flow in two ways:
The main idea of this approach is to use HTTP protocol only for user authorization, including sending user credentials to the service.
Before the implementation, we need to collect the following information:
After we have all the required data, we can proceed with the flow implementation.
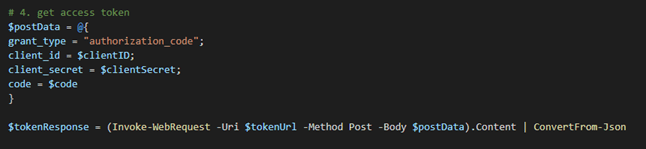
Below I will put an example of the authorization module for Box Service, implemented on PowerShell.
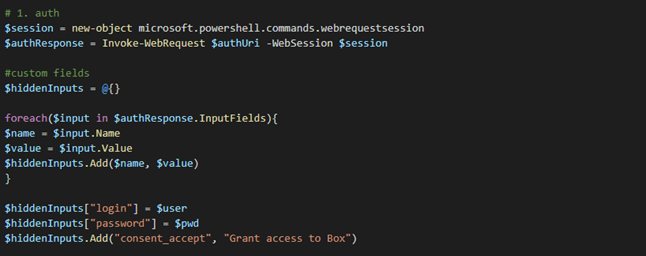
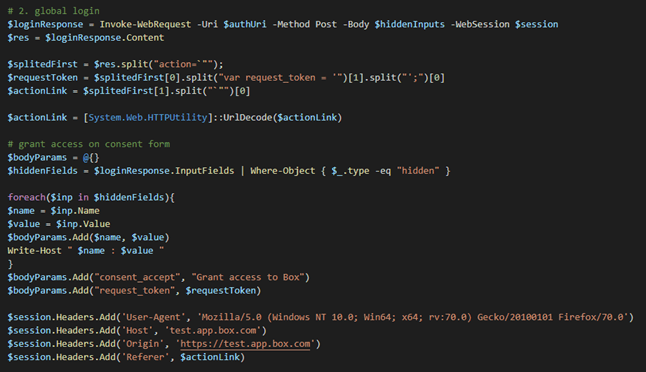
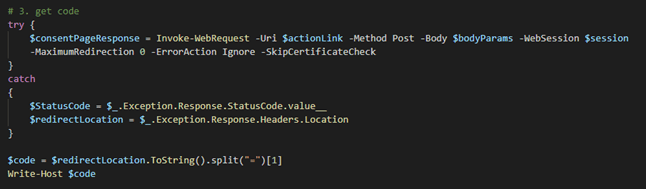
The most time-consuming part of this approach is related to the global user login and consent form, because we need to figure out how to pass user credentials to the request and what headers are required to make the request work.
| PROS | CONS |
|---|---|
| 1. Stability. The script works stable in comparison with the approach, where we interact with a browser. | 1. Time for implementation is quite long due to the features of OAuth2 implementation of a particular 3rd party service. |
| 2. Fast run. Since we do not set up the driver, it saves time during a script run. | 2. Requires sensitive information such as client_secret. |
| 3. Does not require additional settings in CI. |
The main idea is to perform the most time-consuming part of Approach 1 by a web-driver.
The data to collect:
You can find the UML diagram of this approach below:
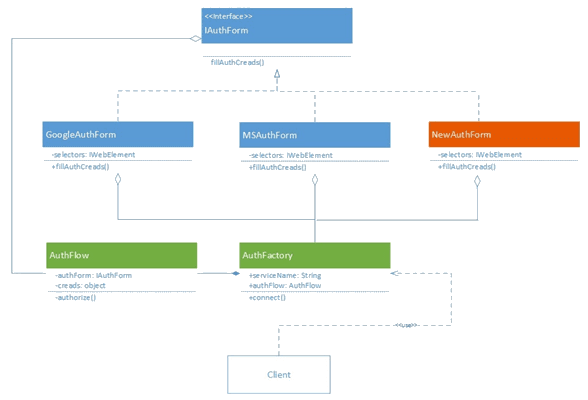
Fig. 1. UML diagram of Approach 2
Here the reusable classes are marked as green. The only thing you need to add to connect a new 3rd party service is the AuthForm page object for a corresponding service (class in orange on Fig. 1).
| PROS | CONS |
|---|---|
| 1. Fast to implement. The most time-consuming part is implemented using a web-driver that makes the implementation process faster. | 1. Can take more time in runtime due to driver setup. |
| 2. Does not require sensitive information like client_secret. | 2. Requires additional containerization in CI. |
| 3. The flow is reusable. | 3. There is a risk of instability of the authorization process due to the driver setup. |
Both approaches have their own pros and cons and can be implemented as a part of a test automation solution. However, let us specify the conditions when we can get more benefits from using each of these approaches.Conclusions
If your project integrates with one 3rd party service, you can use HTTP requests only for authorization. You will spend more time for implementation in comparison with Approach 2, but it will happen just once. In addition, the solution will be stable and fast enough.
If there are two or more integrations with 3rd party services, the best option will be Approach 2, since it saves a lot of time during the implementation of the authorization mechanism.
If you do not have sensitive information or some specific data, required for authorization through the HTTP requests, it is better to use Approach 2 too, because all the attributes, required to send user credentials to the server, are prepared automatically in the browser during UI authorization.

Elena Ozerova is a Senior Test Automation expert and part of an automation initiative group, experienced in desktop- and web-applications automation testing using different technology stacks.
Linkedin profileOAuth 2.0 flow for Web Server applications
Ways of the authorization flow automation

For decades, the manufacturing formula for success was the same – build great equipment, ship to the Client, and get the profit. Now, more OEMs are discovering ...
If you own a product line, run an embedded or connectivity team, or look after the cloud and data stack for connected devices, the EU Data Act probably didn’t a...

At Sigma Software, we constantly explore how emerging technologies can amplify engineering efficiency. Recently, a team from Sigma Software that develops Dovkol...
Would you like to view the site in German?
Switch to German