Defining the SBOM Technical Foundation

USA
Thank you for reaching out to Sigma Software!
Please fill the form below. Our team will contact you shortly.
Sigma Software has offices in multiple locations in Europe, Northern America, Asia, and Latin America.

USA

Sweden

Germany

Canada

Israel

Singapore

UAE

Australia

Austria

Ukraine

Poland

Argentina

Brazil

Bulgaria

Colombia

Czech Republic

Mexico

Portugal

Romania

Uzbekistan
Once organizations adopt SBOMs, the next step is to roll them out across the teams. This is when the initiatives tend to slow down. In many cases, the challenge lies in fitting SBOM practices across product, engineering, and security pipelines. In this article, we describe how to structure SBOM implementation in practice, from selecting the right instruments and formats to embedding SBOM generation into CI/CD workflows and maintaining accuracy over time.
When a local or single-use SBOM pilot can often be created within days, an SBOM designed to meet enterprise security management or regulatory compliance obligations requires deeper preparation and a longer implementation cycle. All because, in this case, the SBOM must scale across systems, teams, and release processes.
However, as organizations begin scaling, they often encounter a typical set of challenges. Those include a lack of visibility into transitive or compiled dependencies, legacy constraints, and inconsistent naming or component versioning. The trick is that these issues are rarely visible during early pilots but become apparent as SBOMs are applied across multiple products, build pipelines, and environments. This is why SBOM implementation needs to be approached as an iterative, system-level effort rather than a one-time technical task.
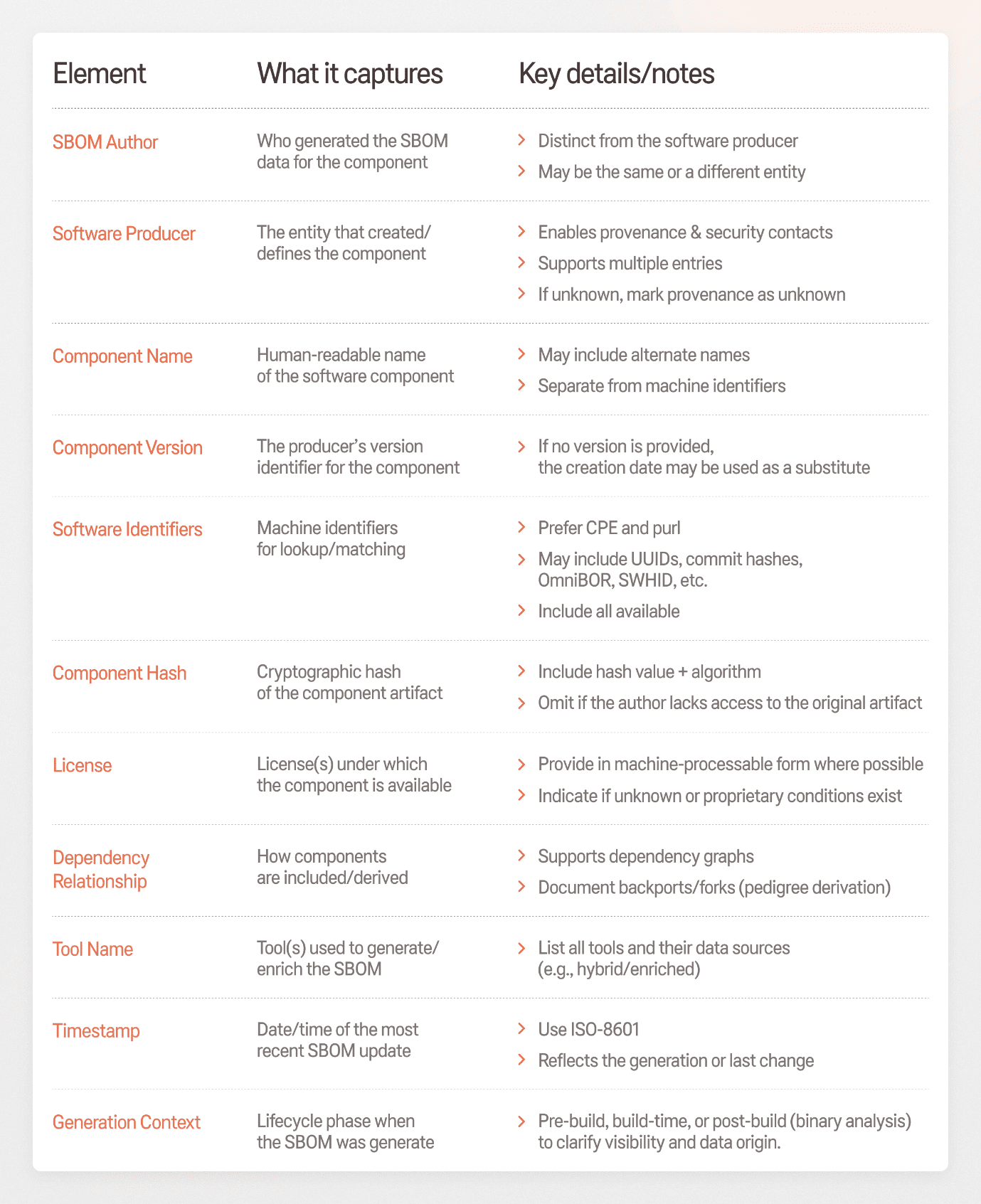
The first step in the SBOM implementation process is establishing a clear technical baseline. This includes defining a consistent set of data fields that allow software components to be identified, dependencies to be traced, and SBOMs to be reliably consumed by automated security and compliance systems.
The table below summarizes the minimum SBOM data fields expected by CISA. These elements, such as SBOM author, software producer, component version, software identifiers, etc., form a consistent, machine-processable foundation. Together, they enable organizations to connect SBOMs with security and license tools and generate them automatically during builds.
In practice, SBOMs adoption helps businesses avoid last-minute issue investigations, gain a clear picture of what software components they actually use, and stay prepared for new security and regulatory requirements. Guidance from organizations such as the NTIA shows that SBOMs help reduce unexpected work, improve visibility into dependencies, and make compliance easier to manage.
Given these advantages, companies tend to use SBOMs in several well-defined operational contexts. The typical use cases of SBOM include:
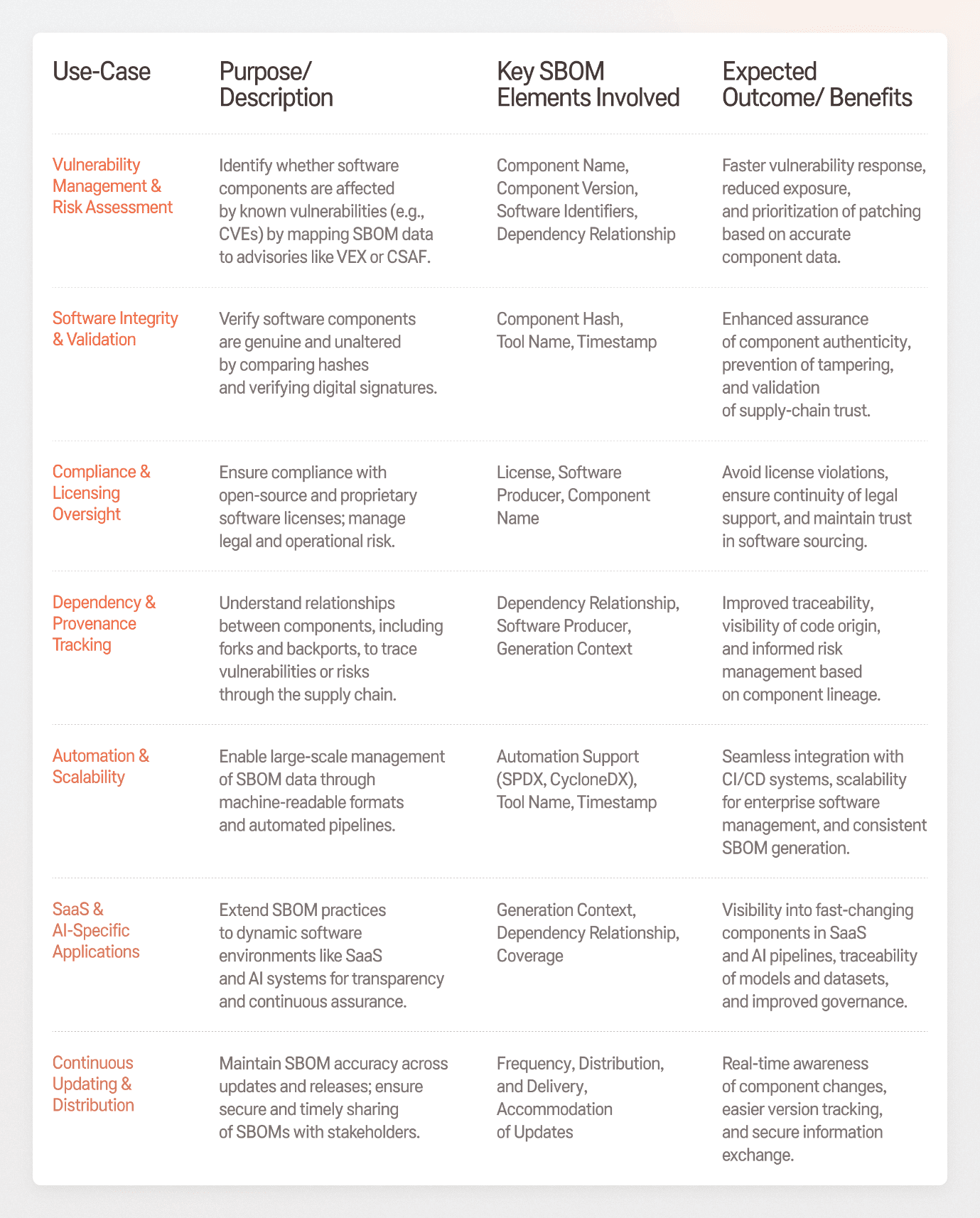
Taken as a whole, these use cases demonstrate that SBOMs become truly valuable when they are used consistently across multiple workflows, enabling organizations to manage software risk, compliance, and change at scale rather than in isolated silos.
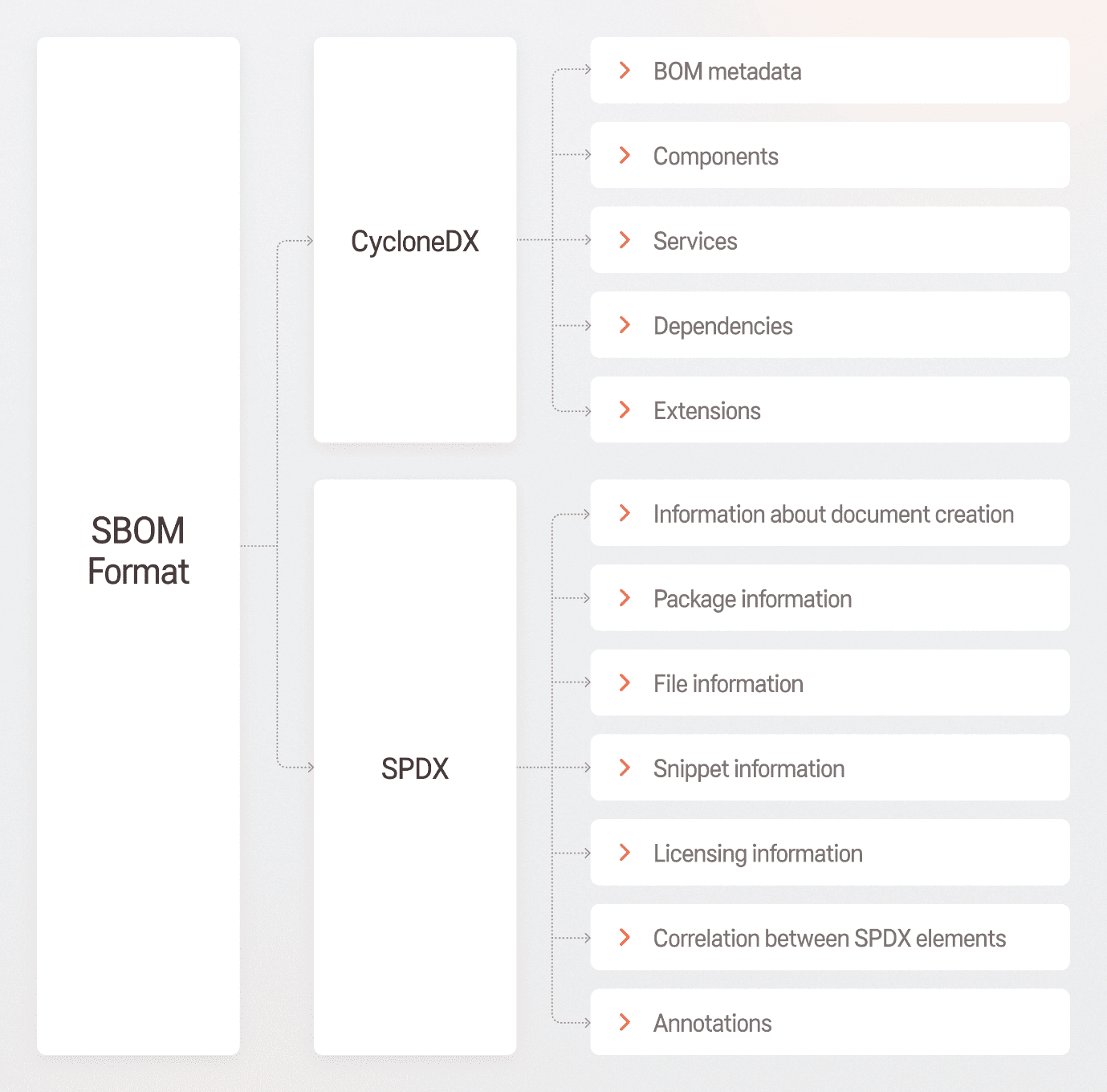
As SBOM adoption expands across teams and processes, organizations need a consistent way to structure and exchange SBOM data. This is typically addressed by selecting a standardized SBOM format such as SPDX or CycloneDX.
The format defines a shared “language” for SBOMs: it specifies which data fields must be present, how components and dependencies are described, and how other tools can reliably read and process the information. Without a common format, SBOMs become difficult to reuse, automate, or share across teams and external partners. The choice of SBOM format depends on what the organization needs SBOMs for, so let’s take a close look at each of them.
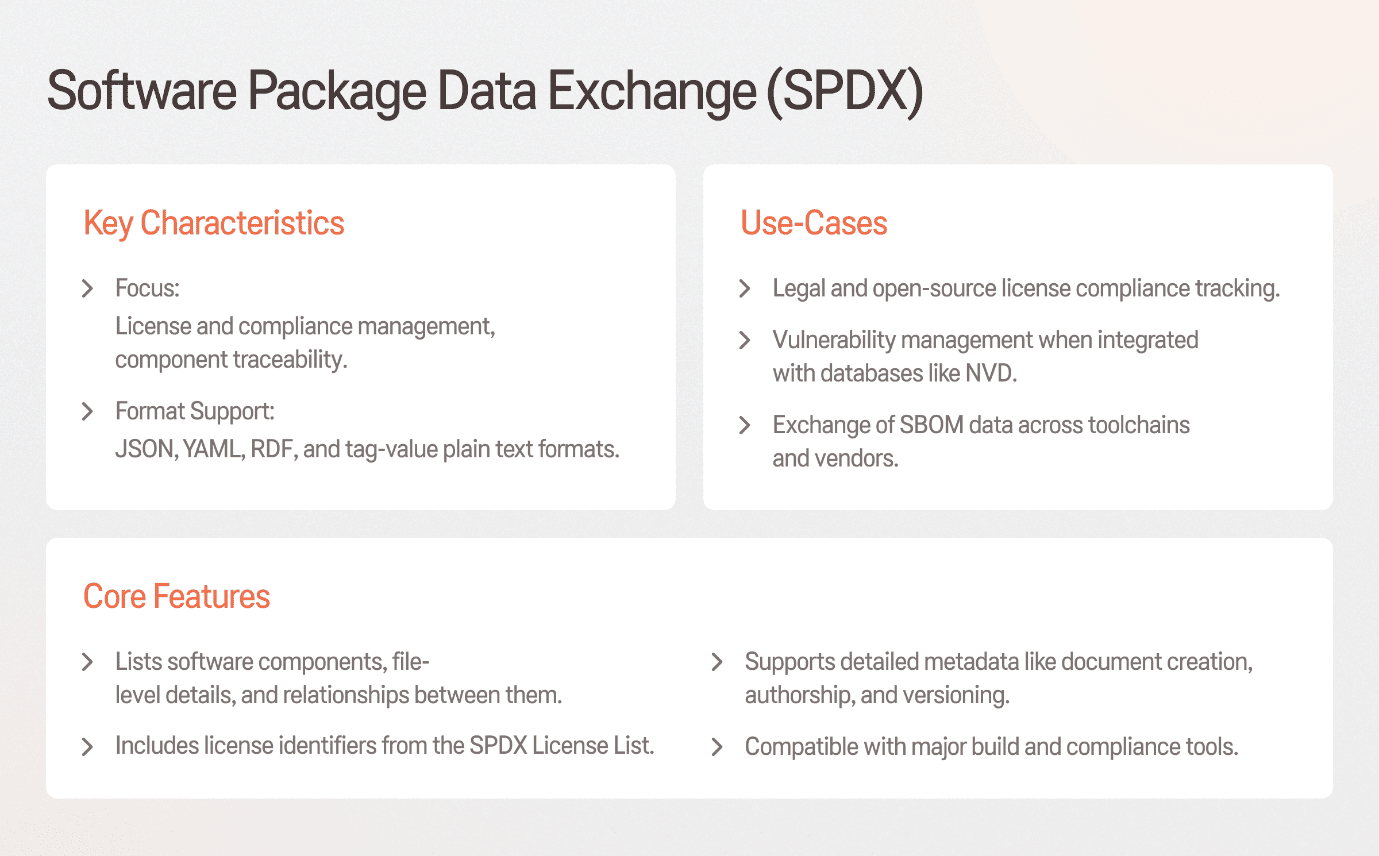
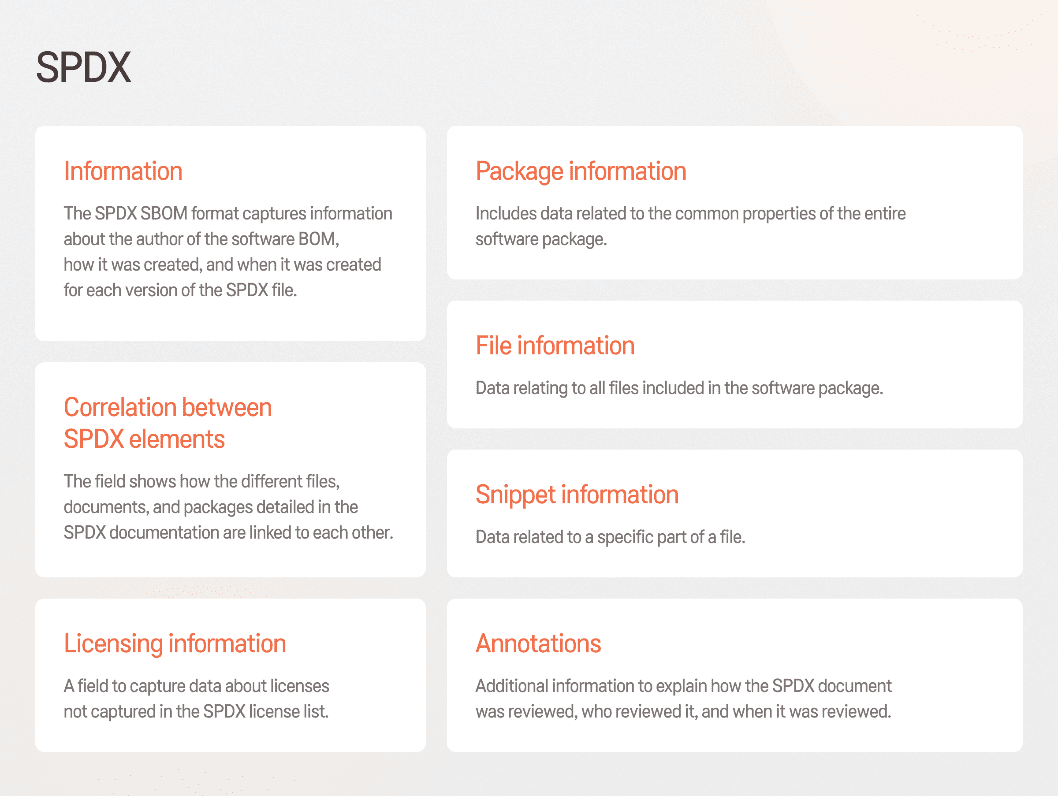
Software Package Data Exchange (SPDX) is an open-source, machine-readable SBOM initiative developed by the Linux Foundation. Its prior goal is to promote compliance and transparency in managing both open-source and proprietary code within development teams and corporate environments. That is why SPDX is usually a better fit for software producers in regulated or contract-heavy supply chains (e.g. automotive, industrial, medical/defense vendors) that must document and audit open-source license/copyright obligations and provenance in a standardized way.
The example below illustrates how an SPDX 2.3 SBOM in JSON captures document metadata (by whom and when it was generated) and a described software package with identifiers, version, supplier, declared/concluded license, as well as depicts a package external reference for traceability:
{
"spdxVersion": "SPDX-2.3",
"dataLicense": "CC0-1.0",
"SPDXID": "SPDXRef-DOCUMENT",
"name": "example-spdx",
"documentNamespace": "http://spdx.org/spdxdocs/example-spdx-3b6b8f41-5a63-4c6a-9bd7-6f6a8e8f2b21",
"creationInfo": {
"created": "2025-11-05T12:00:00Z",
"creators": [
"Tool: ExampleSBOMGen-1.0.0",
"Organization: ExampleCorp"
]
},
"documentDescribes": ["SPDXRef-Package-RootApp"],
"packages": [
{
"name": "root-app",
"SPDXID": "SPDXRef-Package-RootApp",
"versionInfo": "1.2.3",
"supplier": "Organization: ExampleCorp",
"downloadLocation": "NOASSERTION",
"filesAnalyzed": false,
"licenseDeclared": "Apache-2.0",
"licenseConcluded": "Apache-2.0",
"copyrightText": "NOASSERTION",
"externalRefs": [
{
"referenceCategory": "PACKAGE-MANAGER",
"referenceType": "purl",
"referenceLocator": "pkg:npm/root-app@1.2.3"
},In such a way, SPDX gives organizations a clear, auditable view of their software composition, reducing legal risk and simplifying compliance and supplier communication.
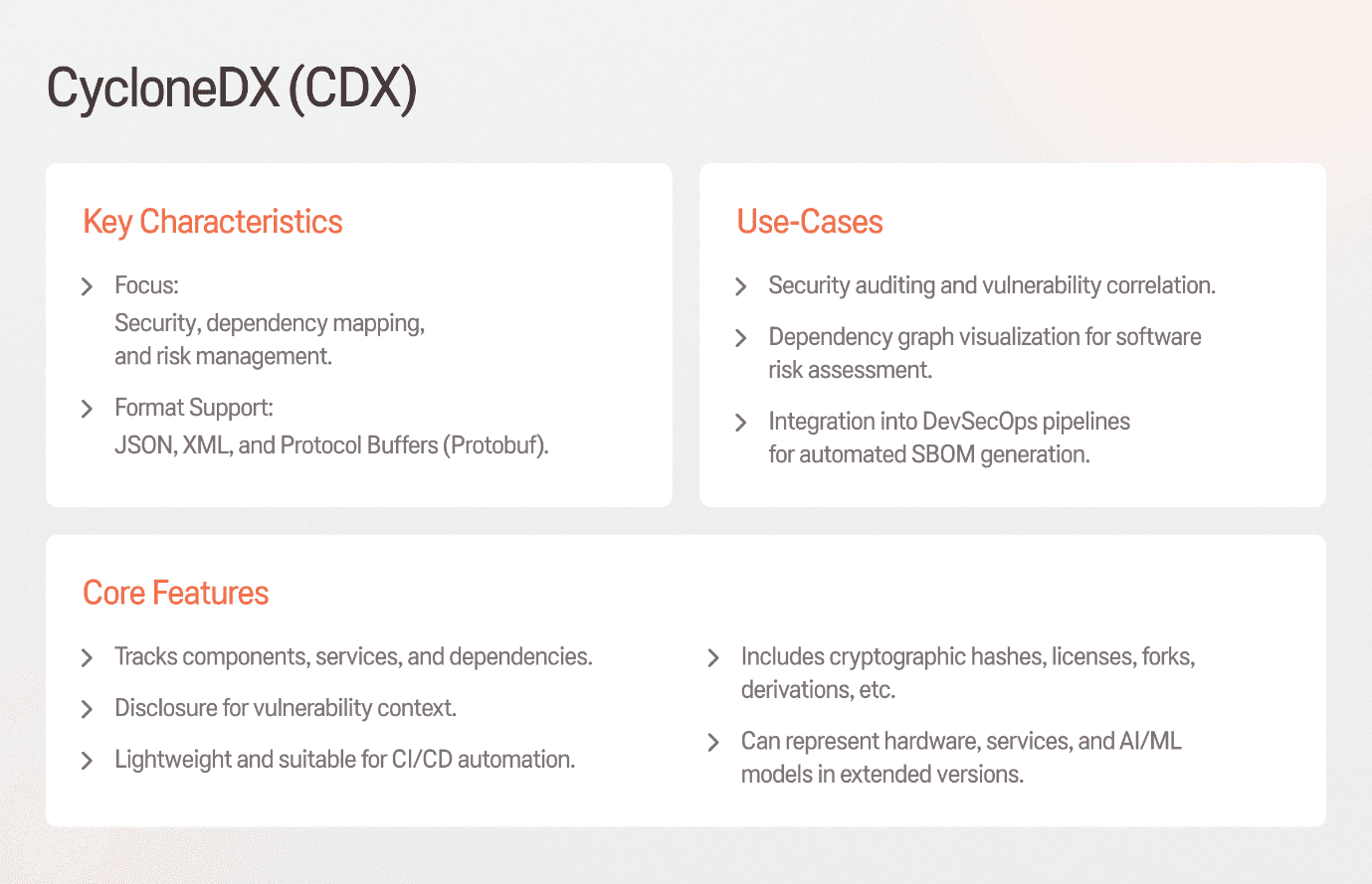
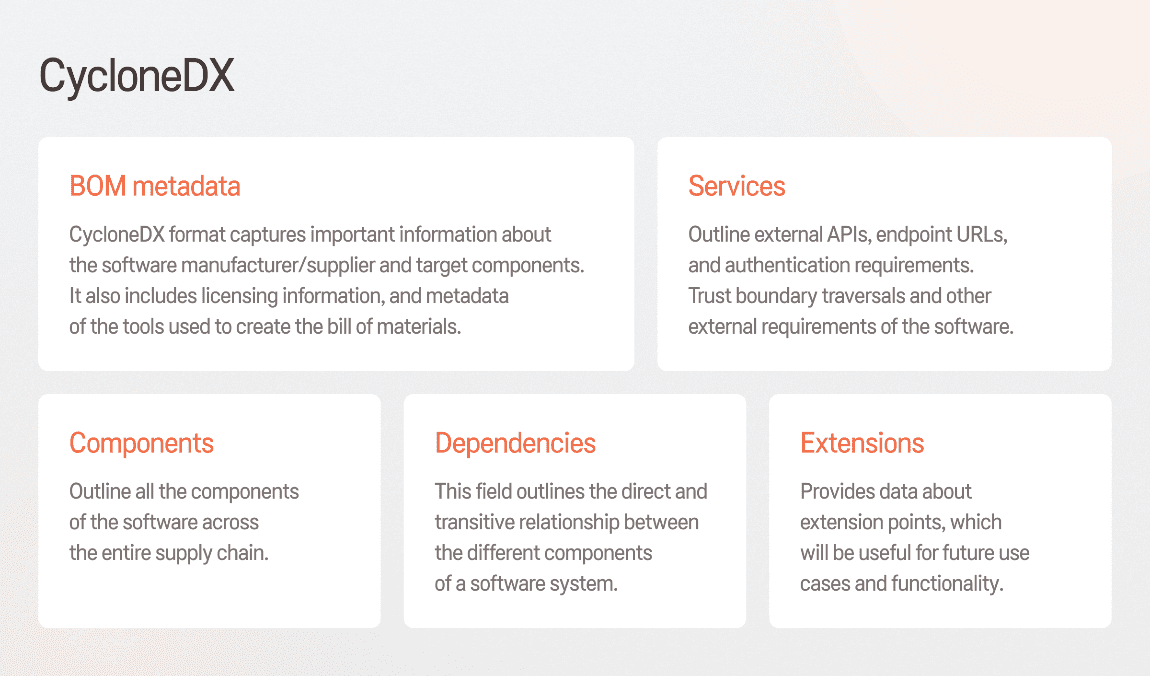
CycloneDX is an open-source SBOM format from the OWASP community, designed with a different data model and implementation focus compared to SPDX.
The key difference between SPDX and CycloneDX lies in their focus. Unlike SPDX, which is typically used as a detailed standard for documenting software, CycloneDX is a lighter, security-focused SBOM format. It is designed for DevSecOps workflows, with an emphasis on vulnerability management and dependency risk analysis. Its lightweight structure makes CycloneDX easier to adopt and well-suited for automated SBOM generation across the software development lifecycle.
In practice, it works like this:
{
"bomFormat": "CycloneDX",
"specVersion": "1.5",
"serialNumber": "urn:uuid:8a9f0a7c-5c3c-4b3a-9a0a-2c0f6b57b7d1",
"version": 1,
"metadata": {
"timestamp": "2025-11-05T12:00:00Z",
"tools": [
{ "vendor": "ExampleCorp", "name": "ExampleSBOMGen", "version": "1.0.0" }
],
"component": {
"bom-ref": "app-root",
"type": "application",
"name": "root-app",
"version": "1.2.3",
"purl": "pkg:npm/root-app@1.2.3",
"licenses": [
{ "license": { "id": "Apache-2.0" } }
]
}
},
"components": [
{
"bom-ref": "lib-lodash",
"type": "library",
"name": "lodash",
"version": "4.17.21",
"purl": "pkg:npm/lodash@4.17.21",
"hashes": [
{ "alg": "SHA-256", "content": "1c3b2a1f0e9d8c7b6a5e4d3c2b1a0f9e8d7c6b5a4e3d2c1b0a9f8e7d6c5b4a31" }
],
"licenses": [
{ "license": { "id": "MIT" } }
],
"externalReferences": [
{ "type": "website", "url": "https://lodash.com" },
{ "type": "distribution", "url": "https://registry.npmjs.org/lodash/-/lodash-4.17.21.tgz" }
]
}
],
"dependencies": [
{
"ref": "app-root",
"dependsOn": ["lib-lodash"]
}
]
}
This example illustrates how a CycloneDX 1.6 SBOM in JSON lists an application’s components and explicit dependency relationships, including package identifiers (purl), hashes, licenses, and external references to support security and supply-chain analysis. For businesses, this enables rapid identification of affected components, automated risk assessment, and more effective security and incident response.
The choice between SPDX and CycloneDX is less about which format is “better” and more about which one aligns with your business priorities and operational context. Both formats are widely adopted and supported, but they are optimized for different use cases.
Thus, SPDX is typically the preferred choice for legal, regulatory, and supplier-facing purposes, while CycloneDX better matches with organizations focused on security operations, vulnerability management, and DevSecOps automation.
However, some enterprises adopt both formats in parallel, using SPDX to satisfy compliance and reporting requirements, while relying on CycloneDX to support day-to-day security and risk management activities.
As SBOMs are used more widely for security and compliance, their formats are evolving to match how modern software is actually built and operated. Earlier versions focused mainly on listing components, but newer versions of SPDX and CycloneDX can also describe complex systems, dependencies, and software lifecycle context.
This shift turns SBOMs from static component lists into practical, automated records that support security, compliance, and supply-chain management. For businesses, this means SBOMs can be reused across tools and processes, provide better traceability, and support day-to-day operational decisions at scale.
SBOM adoption can feel complex, but with a structured plan that defines ownership, it becomes a manageable and valuable part of everyday software operations.
That is why the most effective way to approach SBOM implementation is to start small. Begin with a single product, standardize component identifiers, and validate SBOM quality within the CI/CD pipeline. Once it is proved reliable and useful, the approach can be extended to other products.
If you are ready to start your SBOM implementation journey and need support navigating decisions and setup, we are here to help. Our cybersecurity experts will help you define the right scope, processes, and tooling to navigate these processes while avoiding common pitfalls.

Sigma Software Group provides IT services to enterprises, software product houses, and startups. Working since 2002, we have build deep domain knowledge in AdTech, automotive, aviation, gaming industry, telecom, e-learning, FinTech, PropTech. We constantly work to enrich our expertise with machine learning, cybersecurity, AR/VR, IoT, and other technologies. Here we share insights into tech news, software engineering tips, business methods, and company life.
Linkedin profile
Most AI assistant deployments start with a question: what can we give this system access to? The more data, the better the answers. That logic is correct – and ...

Biotech executives face a massive data problem. The issue is not gathering information. The issue is making that information useful. Clinical trials slow down b...

Healthcare leaders need to switch from billing for services to getting paid for patient health. Artificial intelligence offers specific tools to manage this shi...
Would you like to view the site in German?
Switch to German